In its 14th annual Global Information Security Survey, Ernst & Young found that companies rushing to digitise their businesses with new technologies are increasingly leaving their ability to tackle new and complex security threats behind.
“Information security needs to be more visible in the board room with a clearly defined strategy that will support the business,” said Gerry Chng, IT Risk and Assurance Partner, Ernst & Young Advisory Pte. Ltd.The global survey involved 1,700 organisations in 52 countries and was conducted between June and August 2011.
Although companies are moving into the increasingly borderless world of cloud computing and social media, information security is still not a boardroom priority for most companies and is not a visible agenda for them.
“Security must be carefully planned and take into consideration the practicality of the controls that considers the IT operations. There needs to be buy-in from the business functions, and support needs to come from the top,” Chng added.Only 51% of the survey stated that they have a documented information security strategy. 12% of the respondents present information security topics at each board meeting and fewer than half (49%) of respondents believe that their information security function is meeting the needs of the organization.
With the consumerisation of enterprise IT, organisations have had to allow employees to use personal tablets to access corporate information.
“There are existing solutions in the market that support the secure access of information on personal smartphones and tablets. Organizations should evaluate whether these solutions meet their needs, rather than using traditional channels such as web interfaces and opening up email access via the web as an option.”It was therefore natural that more than half the survey respondents ranked this adoption the second-highest on the list of technology challenges.
Policy adjustments and awareness programs are the top two measures used to address risks posed by this new mobile technology.
The adoption of security techniques and software, however, is still low. For instance, encryption techniques are used by fewer than half (47%) of the global organisations.
The massive popularity and growth of social media has also threatened the IT risk landscape. Social media risks include the introduction of malicious software lurking within social networks, hacked accounts that are used to solicit information, and the release of confidential or negative company information or personal data.
“The traditional paradigm of security within a perimeter is no longer valid.”To address potential risks posed by social media, organizations seem to be adopting a hard-line response. A majority (53%) of the global organizations respond by blocking access to sites rather than embracing the change and adopting enterprise-wide measures.
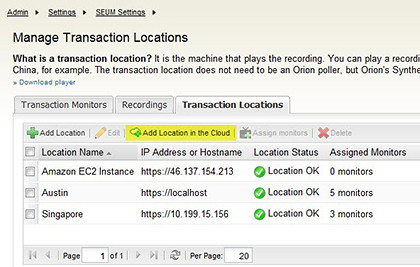
“With the increased collaboration with upstream and downstream partners, data resides not just within the confines of the organization.”Despite all the hype about cloud computing, many organisations are still unclear of the implications of cloud computing. From the survey, 48% of the global respondents said that the implementation of cloud computing is a difficult challenge, and more than half of them (52%) have not implemented any controls to mitigate the risks associated with cloud adoption.
The most frequently taken measure is stronger oversight on the contract management process with cloud providers, but even this is done by only 22% of respondents.
“Confronted with diminishing borders, cloud services, and increasing support of personal tablets for information mobility, companies are asking themselves how to respond to new and emerging risks and whether their strategy needs to be revisited. The focus must move from short-term fixes to a more holistic approach integrated with long-range strategic corporate goals.”The good thing is that companies are aware of the widening gap between business needs and information security – and are willing to address the situation.
72% of the respondents in the survey see a rising level of risk due to increased external threats.
At the same time, more than half (59%) of them plan to increase their information security budgets in the coming 12 months, focusing on areas including business continuity capabilities (47%), data leakage and data loss prevention (28%), compliance monitoring (21%), and identity and access management (21%).
Gerry Chng observes that “there is generally a slow uptake of public cloud services for larger enterprises due to risk concerns. Such services may make sense for a small company as the utility model of the cloud means that these companies do not need to have the capital and operational expenses to maintain their own infrastructure and applications.”
“For larger organizations, the risks of compromising the integrity of sensitive data far outweighs the benefits they may reap from cloud computing. The concept of cloud computing is centered around easy access to data, without the need for knowledge on where the data is stored and how the cloud works,” Chng added
“This lack of specific details makes it difficult for organizations to assess the risks to their data residing in the cloud. In the absence of clear guidance, many organizations seem to be making ill-informed decisions, either moving to the cloud prematurely and without appropriately considering the associated risks, or avoiding it altogether,” concluded Chng.




 Out-of-the-box standardized processes allow IT organizations to deliver Vblock Infrastructure Platforms as a service.
Out-of-the-box standardized processes allow IT organizations to deliver Vblock Infrastructure Platforms as a service.
 Honor customers will get access to Huawei’s ClooudDrive, which will be available in Singapore by end Q1 2012.
Honor customers will get access to Huawei’s ClooudDrive, which will be available in Singapore by end Q1 2012.