Posts Tagged ‘byline’
Friday, June 17th, 2022
What is the key to understanding the depth of an Artificial Intelligence (AI) algorithm’s unique power? Jeff Harris from Keysight Technologies shares his insights into how measurement determines the potential of your AI algorithm.

Determining the potential of your AI algorithm begins with measurement.
At the core of every AI algorithm are three basic ingredients:
- the ability to measure
- knowing how much of what you measure needs to be processed
- the ability to process more than one input at a time
To what depth a system can measure can be thought of as its potential.
Determining what aspects of those measurements must be sent to the processor can be thought of as delivering that potential.
Finally, knowing how to combine the salient parts of those measurements in the correct proportions, known as sensor fusion, is the key to exploring an algorithm’s IQ or reasoning potential.
(more…)
Tags:AI, Artificial Intelligence, byline, commentary, interviews, Keysight, opinion, Tech Focus, technology
Posted in AI, Interview, Interview, Keysight, Opinion, Tech Focus | 2 Comments »
Friday, May 20th, 2022
We frequently see DDR SDRAMs as a key specification of computers and digital devices. In this two-part guest commentary, Ben Miller from Keysight Technologies shares his insights into the design of DDR SDRAMs (Part 1) and how faster memory speeds shape the future (Part 2).
DDR5 is still in the early phases of adoption. JEDEC released the standard in July 2020. The first CPU platform to support DDR5 was released in early 2022.
However, this platform still includes DDR4 support, so it could be some time before the industry accepts DDR5 as the de-facto memory standard and fully transitions memory systems to the new standard.
Faster memory enables the future
Over the next couple of years, more personal computers, servers, and embedded systems will take advantage of the higher speed, lower power, and greater memory capacity available with DDR5.
(more…)
Tags:byline, commentary, DDR, interviews, Keysight, memory, opinion, RAM, SDRAM, Tech Focus, technology
Posted in Brief, Business IT, Enterprise IT, Interview, Keysight, Opinion, Tech Focus, Technology | 2 Comments »
Thursday, May 19th, 2022
We frequently see DDR SDRAMs as a key specification of computers and digital devices. In this two-part guest commentary, Ben Miller from Keysight Technologies shares his insights into the design of DDR SDRAMs (Part 1) and how faster memory speeds shape the future (Part 2).
Faster data processing requires faster memory.
Double data rate synchronous dynamic random-access memory (DDR SDRAM) enables the world’s computers to work with the data in memory.
Faster, not wider
Since the origins of SDRAM, engineers have faced challenges with increasing memory speeds.
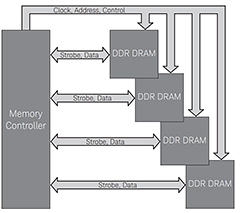
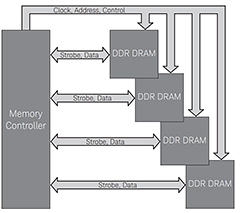
Figure 1: DDR has both one-way control signals and bidirectional data buses. Click to enlarge.
DDR emerged as a faster, more efficient way to handle memory, while providing a universal standard between chip designers and device manufacturers.
As shown in Figure 1, DDR memory consists of a memory controller which transmits clock, address and control signals, and a series of DRAM chips which store the data.
In a write operation, the controller sends data and strobe signals to the DRAM; in a read operation, the DRAM sends data and strobe signals back over the same bi-directional line.
DDR SDRAM became the standard in the late 1990s and has since been improved upon many times over.
Prior to DDR, memory speeds maxed out in the range of 100 MT/s.
(more…)
Tags:byline, commentary, DDR, interviews, Keysight, memory, opinion, RAM, SDRAM, Tech Focus, technology
Posted in Brief, Enterprise IT, Interview, Keysight, Opinion, Tech Focus, Technology | 3 Comments »
Wednesday, April 20th, 2022
The pace of wireless innovation is accelerating to enable faster, more responsive, and more reliable connections worldwide. In this guest commentary, Eric Hsu from Keysight Technologies shares his insights on how the wireless communications industry is ready for significant technology changes across multiple systems.

A multichannel test solution with a Keysight M9484C VXG four-channel vector signal generator and a four-port oscilloscope.
While cellular communication is transitioning from 4G to 5G to enable extreme data throughputs, satellite communications providers are building networks in space to provide high-speed communications from anywhere in the world.
Wireless engineers look for breakthrough technologies to maximise system throughput, robust links, and data handling capabilities.
The key technology components of the wireless system physical layer are
- wider signal bandwidths
- higher-order modulation schemes
- multi-antenna techniques
(more…)
Tags:byline, commentary, interviews, Keysight, opinion, Tech Focus, technology, wireless
Posted in Business IT, Enterprise IT, Interview, Keysight, Network, Opinion, Tech Focus, Wi-Fi | No Comments »
Thursday, April 14th, 2022
You may be familiar with Observability, or the measurement of internal states of a system by examining its outputs. Deep Observability extends the inside-out approach of traditional Observability with an outside-in perspective to leverage actionable network-level intelligence to secure and efficiently manage hybrid and multi-cloud IT environments.
* In today’s expert contribution, Simon Lee from Gigamon shares his insights into the market readiness for Deep Observability as well as Gigamon’s strategies and outlook for 2022.

Simon Lee, Vice President, Asia Pacific and Japan, Gigamon
Despite the challenges from the pandemic, Gigamon Asia Pacific exited 2021 with strong double-digit growth.
We saw this as a positive market signal from customers on the criticality of leveraging actionable network-level intelligence to secure and efficiently manage their hybrid and multi-cloud IT environments.
Riding on this momentum, we are optimistic about our growth prospects for 2022.
(more…)
Tags:byline, cybersecurity, Gigamon, interviews, network, networking, opinion, security
Posted in Business IT, Enterprise IT, Interview, Network, Opinion, Security | No Comments »
Monday, April 27th, 2020
The COVID-19 pandemic is spurring the healthcare industry to turn to robots for help. Darrell Adams shares how cobots – collaborative robots – reduce the risk of healthcare workers by minimising in-person contact with patients who are isolated.
* Darrell Adams is the Head of Southeast Asia & Oceania at Universal Robots.

A UR5 cobot collaborating with a healthcare worker.
COVID-19, the global pandemic, took the world by surprise and suddenly the healthcare system has to confront one of the toughest challenges on a global scale.
Millions of Nurses Needed
The global healthcare system is cracking under the strain of this global pandemic.
Yet, a recent report shows that globally, we are in need of 6 million more nurses to achieve global health targets, even without a global pandemic.
This is an alarming number, and it is unlikely that over a short period of time, the demand can be met.
Healthcare workers are working round the clock and the intense workload at the frontline led to exhaustion in many, virus infection in others, and some sadly passed away in their line of duty.
Human Factors and Errors
In the study of human factors and fatigue, factors which contribute to human errors within the confines of human factors include sleep deprivation, shift schedules, repetitive tasks, physically demanding tasks, and of course, stress.
In the medical sector, besides the lack of nurses, the healthcare industry faces other challenges such as a high instance of human error due to a pressurising and non-automated environment, working on shifts, with a substantial amount of time dedicated to administrative tasks, which takes away precious time from patient care.
(more…)
Tags:byline, cobots, healthcare, robots, Tech Focus
Posted in Brief, Enterprise IT, Healthcare, Robots, Tech Focus | No Comments »
Saturday, June 11th, 2016
As a follow up on the opinion piece that Tony Jarvis contributed yesterday on Endpoint Protection, I asked him to share his take on the Singapore Government’s move to cut Internet access from work computers used by civil servants from May next year.

Tony Jarvis is the Chief Strategist (Asia, Middle East and Africa) for Check Point Software Technologies.
Below are some of his personal views
Question: Is banning internet the right approach to securing government?
There is no right or wrong approach around banning the Internet.
At first glance, the decision to ban Internet access might seem extreme.
Background
The Singapore Government is cutting off Internet connections from work computers used officially by public servants from May 2017, in an effort to plug potential leaks from work emails and shared documents – amidst today’s advanced security threats.
Employees can still surf the Web on their personal smartphones and tablets since these devices are not connected to the government network.
Dedicated Internet terminals will be issued to those who need them in work.
However, it is important to note that this decision will have been made after careful review, taking into consideration a number of factors.
For example, removing access to the Internet will bring with it the benefit of reducing exposure to many threats.
Unfortunately, this comes at the expense of the productivity and effectiveness of the organisation and its employees.
These are policy decisions made by organisations, in this case, the government, and we are certain that they have considered multiple aspects.
This particular case highlights the ongoing challenge organisations have remaining secure in a connected world.
(more…)
Tags:byline, Check Point, civil service, endpoint, Government, guest blog, Hyperwise, Internet, interview, opinion, security, Singapore, Tony Jarvis
Posted in Business IT, Interview, Opinion, Security | No Comments »
Friday, June 10th, 2016
The Singapore Government is cutting off Internet connections from work computers used officially by public servants from May 2017, in an effort to plug potential leaks from work emails and shared documents – amidst today’s advanced security threats.
I invited Tony Jarvis from Check Point Software Technologies to share his opinion on how best to secure an organisation’s network and IT assets. This guest blog is written by him.

Tony Jarvis is the Chief Strategist (Asia, Middle East and Africa) for Check Point Software Technologies.
With every detection of a new threat, the security landscape evolves and attackers are no longer just looking at inventive ways to infiltrate a network but also innovative evasion techniques and the damage it will inflict.
“To say the security landscape is constantly changing would be an understatement,” says Tony Jarvis, Chief Strategist (Asia, Middle East and Africa) for Check Point Software Technologies.
What really matters is how vendors respond to the ever-evolving landscape and not just make incremental enhancements to existing solutions that still predominantly focus on detection, rather than prevention.
With the numerous acquisitions and layoffs being announced, the real question that CIOs and CISOs need to ask is: “Is my security vendor in for the long run?”
Central to any effective security strategy is the ability to stop threats before the initial compromise.
The only way to do this is with prevention.
Many vendors simply can’t do it, which is why they talk about detection.
I also asked Tony specifically for his take on the Singapore Government’s move to cut Internet access from work computers used by civil servants from May next year.
Here are more of his opinions in a Q&A format.
The majority of solutions being deployed today rely on a detection capability, with some requiring users to choose whether infected files should be quarantined or allowed to pass through.
Not only is this intrusive to the user experience, it’s also prone to human error.
Inflexible deployment models calling for an all or nothing use of cloud or private malware analysis fail to meet many customers’ requirements.
To make matters worse, the sandboxing process often takes too long, giving malware plenty of time to get to work before its presence becomes known.
(more…)
Tags:byline, Check Point, civil service, endpoint, Government, guest blog, Hyperwise, Internet, interview, opinion, security, Singapore, Tony Jarvis
Posted in Enterprise IT, Interview, Opinion, Security | No Comments »
Thursday, May 26th, 2016
Jimmy Fitzgerald – Vice President of Asia Pacific & Japan at ServiceNow – shares six ways to help your employees work smarter, not harder. This guest blog was contributed by Fitzgerald.

Jimmy Fitzgerald’s team at ServiceNow helps customers to eliminate reliance on email, spreadsheets and other manual processes so their employees can work smarter, not harder.
In recent years, online retail platforms such as Zalora have truly streamlined their processes of browsing, checkout and payment, wooing shoppers with their speed, efficiency and superior user experience.
Consumers in Singapore now hold speedy deliveries and seamless experiences as the standard when they shop online.
(more…)
Tags:byline, guest blog, Jimmy Fitzgerald, opinion, ServiceNow
Posted in Business IT, Enterprise IT, Howtos, Interview, Opinion, Reference, Tips | No Comments »
Wednesday, July 1st, 2015
Shaun Wormald, Senior Director of Unified Communications, InterCall Asia Pacific shares six ways to boost meeting productivity during video conferences. This guest blog was contributed by Wormald.

Shaun Wormald, Senior Director of Unified Communications, InterCall Asia Pacific.
The benefits of using video conferencing solutions from an organisational perspective is very clear – it helps businesses achieve their targets while being cost efficient.
While these bottom lines and costs may not directly concern you as an end user, video conferences can actually work to your advantage and help you accomplish tasks – if you know how to do them right.
Six tips to enhance video conferencing efficiency
- Be prepared
- Be early and test the application
- Join the video conference, then mute your microphone
- Speak clearly but don’t shout
- Make yourself presentable
- Focus
To help you realise how prevalent video conferences are in a business setting, a recent Research and Markets study reports that the global video conferencing market is expected to reach US$ 6.40 billion by 2020.
Asia Pacific also sees a similar trend.
While it’s tempting to join video meetings in a way that’s convenient for you, doing so affects not only your ability to contribute to the discussion, but also those of the other attendees.
This wastes what could have been a great opportunity to collaborate.
To make sure your next video conferences will be productive, may I share some tips with you below.
(more…)
Tags:byline, guest blog, InterCall, opinion, Shaun Wormald, UC, unified communications
Posted in audioVisual, Brief, Business IT, Enterprise IT, Interview, Opinion, Technology, Video | No Comments »












Tech Focus: Measurement Determines the Potential of Your AI Algorithm
Friday, June 17th, 2022What is the key to understanding the depth of an Artificial Intelligence (AI) algorithm’s unique power? Jeff Harris from Keysight Technologies shares his insights into how measurement determines the potential of your AI algorithm.
Determining the potential of your AI algorithm begins with measurement.
At the core of every AI algorithm are three basic ingredients:
To what depth a system can measure can be thought of as its potential.
Determining what aspects of those measurements must be sent to the processor can be thought of as delivering that potential.
Finally, knowing how to combine the salient parts of those measurements in the correct proportions, known as sensor fusion, is the key to exploring an algorithm’s IQ or reasoning potential.
(more…)
Tags:AI, Artificial Intelligence, byline, commentary, interviews, Keysight, opinion, Tech Focus, technology
Posted in AI, Interview, Interview, Keysight, Opinion, Tech Focus | 2 Comments »