Did you know that sex toys could be connected to the Internet, to a smartphone or to another sex toy? Along with the technology that makes sex toys smart, vulnerabilities are introduced that could endanger the user’s data, privacy and even safety!
With the emergence of the IoT, many manufacturers have entered the sexual pleasure market by integrating the ability to control devices through mobile apps as well as adding web-based interconnectivity.
There are currently numerous different apps available, each of which offers the ability to control a wide range of models.
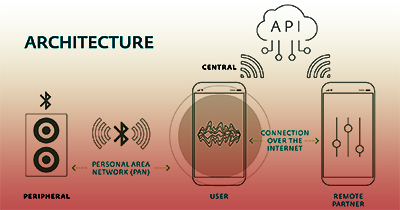
In terms of their architecture, most of these devices can be controlled via Bluetooth Low Energy (BLE) from an app installed on a smartphone.
Sex in the Digital Era
ESET has published a White Paper on their study on the potential security and safety flaws of connected sex toys.
The title of the report is “Sex in the Digital Era – How secure are smart sex toys?” and here is an excerpt on the characteristics of sex toys.
The main advantages of this protocol are that it has very low power requirements, communications are within an acceptable range, there is interoperability among chipset manufacturers, and it all comes in a very compact size.
As a result, a lot of smart devices for the home, health, car, and even sex toy fields, use BLE between the device and the app that controls it.
Like Bluetooth, BLE operates on the 2.4 GHz ISM band.
However, unlike standard Bluetooth, BLE stays in sleep mode all the time, except when a connection is initiated.
Also, the actual connection times themselves are just a few milliseconds, unlike Bluetooth, which takes more than 100 milliseconds.